In a world where screens dominate our lives but the value of tangible printed materials hasn't faded away. Be it for educational use or creative projects, or simply adding an extra personal touch to your space, Bootstrapmade Vulnerabilities are now a useful resource. For this piece, we'll dive in the world of "Bootstrapmade Vulnerabilities," exploring the benefits of them, where to find them and how they can add value to various aspects of your daily life.
Get Latest Bootstrapmade Vulnerabilities Below
Bootstrapmade Vulnerabilities
Bootstrapmade Vulnerabilities - Bootstrapmade Vulnerabilities, Vulnerability Vs Malware, What Is Exploitable Vulnerability, What Is Vulnerabilities
Issue description After the execution of command npm install save bootstrap 4 1 1 I got the following error bootstrap 4 1 1 added 202 packages from 89 contributors removed 165 packages and
Bootstrap v3 1 11 and v3 3 7 contain a cross site scripting XSS vulnerability via the Title parameter in vendor views add product php The NVD provides CVSS scores CWE ID
Bootstrapmade Vulnerabilities include a broad assortment of printable, downloadable material that is available online at no cost. They are available in numerous forms, like worksheets coloring pages, templates and more. The attraction of printables that are free is in their variety and accessibility.
More of Bootstrapmade Vulnerabilities
Salesforce Is Investigating Impact Of Spring4Shell Vulnerabilities DYDC

Salesforce Is Investigating Impact Of Spring4Shell Vulnerabilities DYDC
Bootstrap versions prior to 3 4 1 and 4 3 1 are vulnerable to Cross Site Scripting XSS due to missing input sanitization The advisory provides details
Snyk scans for vulnerabilities in both your packages their dependencies and provides automated fixes for free Scan for indirect vulnerabilities Go back to all versions of this
Bootstrapmade Vulnerabilities have gained immense popularity due to a variety of compelling reasons:
-
Cost-Effective: They eliminate the requirement to purchase physical copies or costly software.
-
The ability to customize: There is the possibility of tailoring printing templates to your own specific requirements such as designing invitations or arranging your schedule or decorating your home.
-
Educational Use: Printables for education that are free provide for students from all ages, making them a useful tool for parents and teachers.
-
The convenience of instant access numerous designs and templates helps save time and effort.
Where to Find more Bootstrapmade Vulnerabilities
How To Use GitLab Security Features To Detect Log4j Vulnerabilities
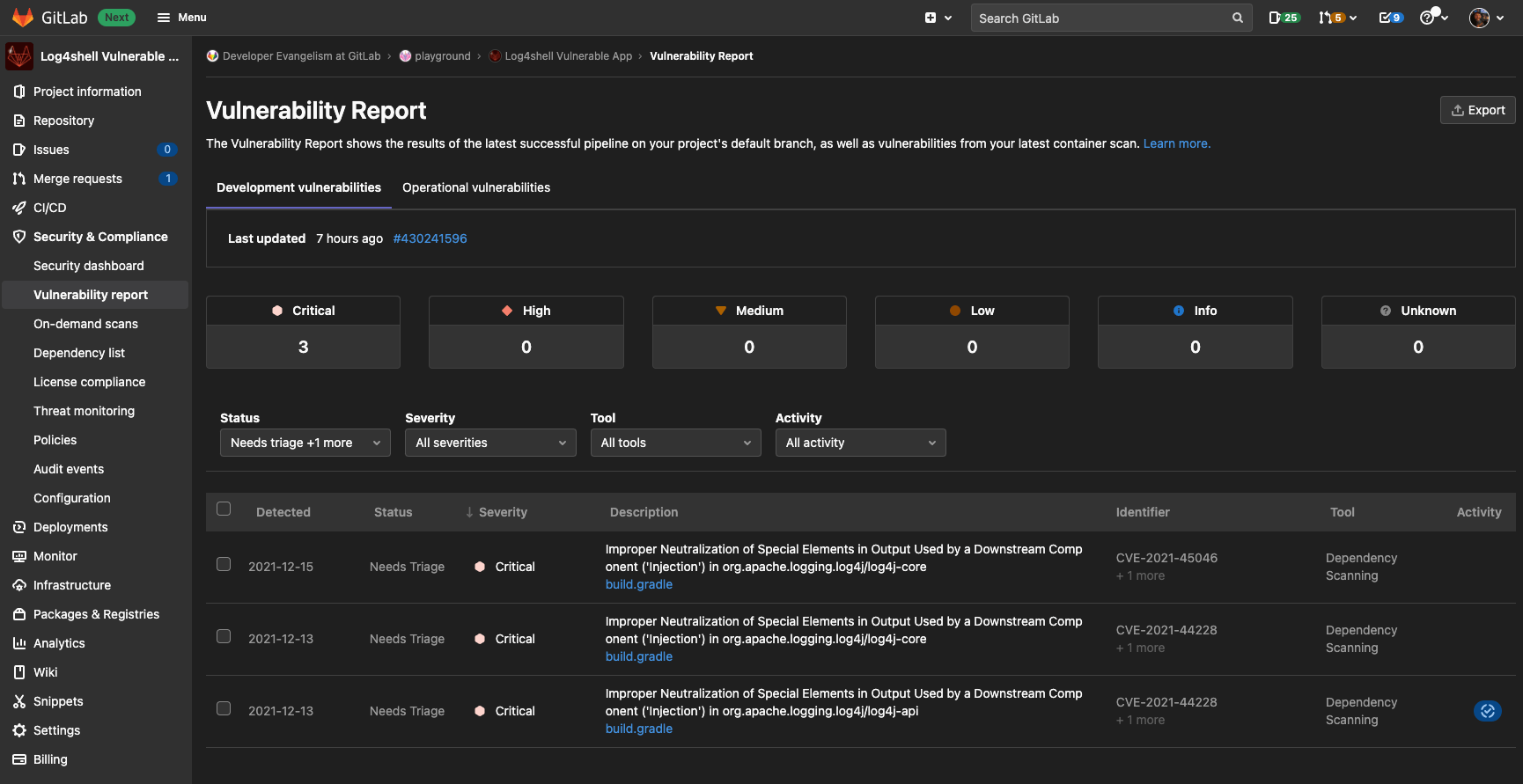
How To Use GitLab Security Features To Detect Log4j Vulnerabilities
Find public repositories that use bootstrapmade templates or frameworks for web development Browse code issues pull requests and stars for various projects
A cross site scripting XSS vulnerability in Bootstrap before 3 4 1 and 4 3 x before 4 3 1 allows an attacker to inject malicious code into the tooltip or popover data
Now that we've piqued your interest in Bootstrapmade Vulnerabilities Let's find out where you can get these hidden gems:
1. Online Repositories
- Websites like Pinterest, Canva, and Etsy provide a wide selection and Bootstrapmade Vulnerabilities for a variety needs.
- Explore categories such as decoration for your home, education, the arts, and more.
2. Educational Platforms
- Educational websites and forums frequently provide worksheets that can be printed for free Flashcards, worksheets, and other educational materials.
- Ideal for parents, teachers as well as students who require additional sources.
3. Creative Blogs
- Many bloggers are willing to share their original designs or templates for download.
- The blogs covered cover a wide range of topics, that includes DIY projects to party planning.
Maximizing Bootstrapmade Vulnerabilities
Here are some ideas in order to maximize the use use of printables for free:
1. Home Decor
- Print and frame gorgeous images, quotes, or decorations for the holidays to beautify your living areas.
2. Education
- Utilize free printable worksheets to enhance your learning at home (or in the learning environment).
3. Event Planning
- Make invitations, banners as well as decorations for special occasions like weddings and birthdays.
4. Organization
- Be organized by using printable calendars checklists for tasks, as well as meal planners.
Conclusion
Bootstrapmade Vulnerabilities are an abundance of fun and practical tools catering to different needs and needs and. Their access and versatility makes they a beneficial addition to any professional or personal life. Explore the endless world of Bootstrapmade Vulnerabilities today and uncover new possibilities!
Frequently Asked Questions (FAQs)
-
Are the printables you get for free completely free?
- Yes, they are! You can download and print these resources at no cost.
-
Can I utilize free printouts for commercial usage?
- It is contingent on the specific terms of use. Always verify the guidelines of the creator before using any printables on commercial projects.
-
Do you have any copyright rights issues with Bootstrapmade Vulnerabilities?
- Certain printables could be restricted on their use. Be sure to read the terms and regulations provided by the designer.
-
How do I print Bootstrapmade Vulnerabilities?
- Print them at home with an printer, or go to the local print shop for high-quality prints.
-
What software do I require to open printables that are free?
- Many printables are offered in PDF format. These can be opened using free software such as Adobe Reader.
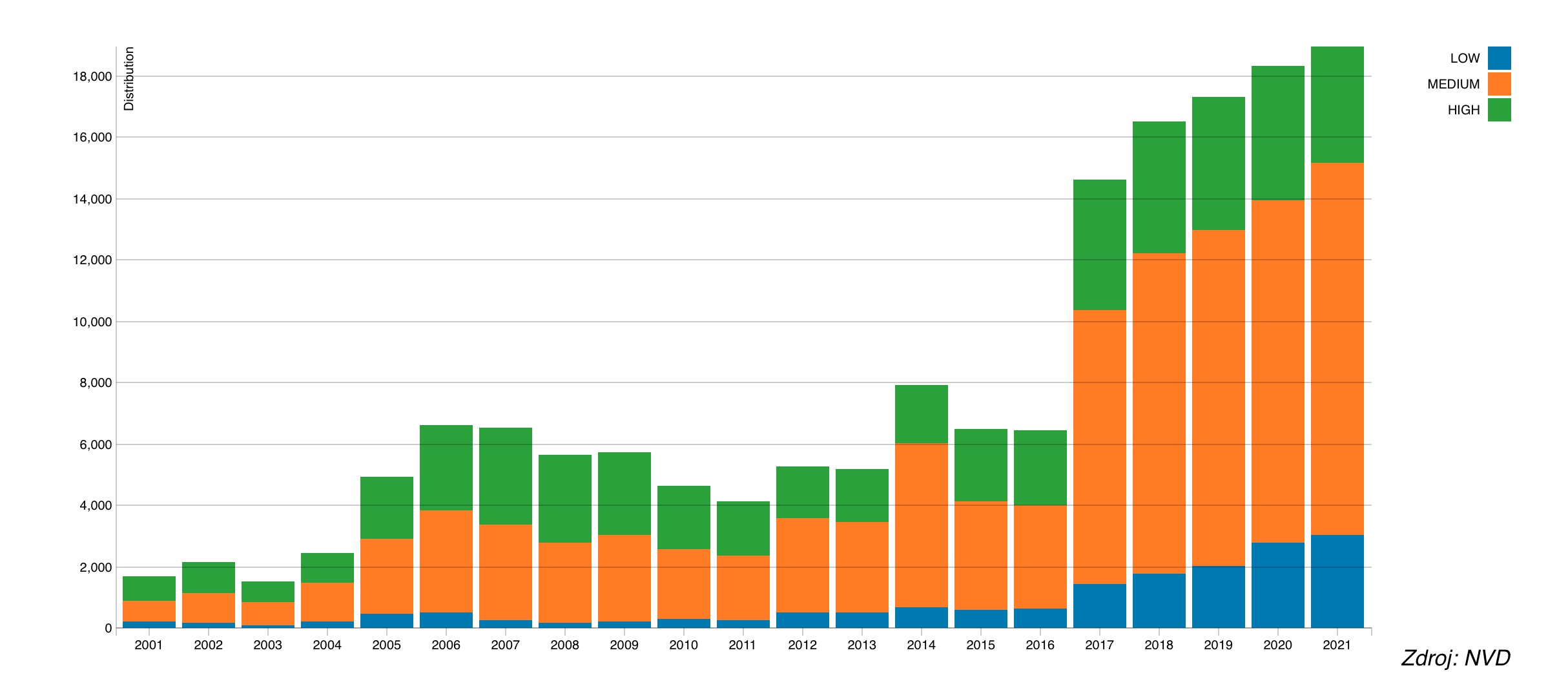
GFI SOFTWARE 2021 WILL BE THE YEAR WITH THE MOST VULNERABILITIES
CISA s Known Exploited Vulnerabilities Catalog Expert Interview Series

Check more sample of Bootstrapmade Vulnerabilities below
GitHub Houssameehsain CutnFill DeepRL Positioning A Building Mass On
CISA Warns For Vulnerabilities In Industrial Control Systems ICS

Log4shell Full Picture All The Vulnerabilities Affecting Log4j

Understanding Wireless Vulnerabilities Jamming Attacks

GitHub Aminyazdanpanah Rush Hour Solver Rush Hour Solver In PHP
Influencers Vulnerabilities Found To Be A Double edged Sword Techno


https://nvd.nist.gov/vuln/detail/CVE-2022-26624
Bootstrap v3 1 11 and v3 3 7 contain a cross site scripting XSS vulnerability via the Title parameter in vendor views add product php The NVD provides CVSS scores CWE ID

https://medium.com/@haydengpt/addressing-new...
HeroDevs has just released patches for three medium risk vulnerabilities that were discovered in Bootstrap 3 and 4 in July 2024 These issues identified as CVE
Bootstrap v3 1 11 and v3 3 7 contain a cross site scripting XSS vulnerability via the Title parameter in vendor views add product php The NVD provides CVSS scores CWE ID
HeroDevs has just released patches for three medium risk vulnerabilities that were discovered in Bootstrap 3 and 4 in July 2024 These issues identified as CVE

Understanding Wireless Vulnerabilities Jamming Attacks

CISA Warns For Vulnerabilities In Industrial Control Systems ICS
GitHub Aminyazdanpanah Rush Hour Solver Rush Hour Solver In PHP

Influencers Vulnerabilities Found To Be A Double edged Sword Techno

Hidden Vulnerabilities In Clinical Workflow Put PHI At Risk

Web3 Industry Faces 1 7 Billion In Losses Salus Reveals Trends And

Web3 Industry Faces 1 7 Billion In Losses Salus Reveals Trends And

How To Find And Fix API Vulnerabilities Noname Security